How to Install RPM Packages on CentOS 8
RPM is a packaging format used by most popular Linux distributions such as CentOS, Red hat, and Fedora. In the official CentOS repository, a large number of packages…
Read More402 articles found
 CentOS
CentOS
RPM is a packaging format used by most popular Linux distributions such as CentOS, Red hat, and Fedora. In the official CentOS repository, a large number of packages…
Read More CentOS
CentOS
Flameshot is used for taking a screenshot that is open-source and available for almost all Linux-based distributions as well as for Windows and macOS. This application is developed…
Read More CentOS
CentOS
System administrators who have used Windows users might be well aware of the Putty application. Putty is a free, open-source, and most popular SSH client used to connect…
Read More CentOS
CentOS
Visual Studio Code is a cross-platform and open-source code editor that is developed by Microsoft. It offers built-in various features in which debugging support, syntax highlighting, embedded Git…
Read More CentOS
CentOS
From the name implies, the head command shows by default the 10 top lines from a file. This command can be piped with other commands to produce standard…
Read More CentOS
CentOS
Mono is a cross-platform framework that is used for developing and operating various applications based on some additional specified standards. It supports .net frameworks and standard API as…
Read More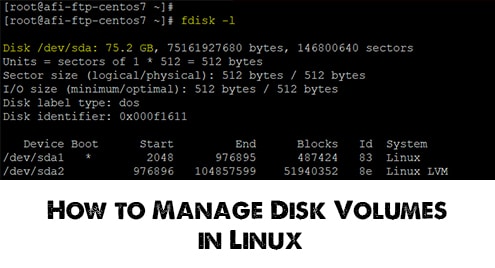 CentOS
CentOS
In this article, we are going to show you the detailed steps to manage your disk volumes. This will include adding or extending the physical hard drives to…
Read More CentOS
CentOS
Docker-decompose tool is commonly used to configure multiple container-based Docker applications. Let’s we can say that Docker-compose is a command-line tool that helps to deploy multiple containers and…
Read More CentOS
CentOS
Apache OpenOffice is known as OpenOffice. It is an open-source office suite that consists of different features such as presentations, word processing, spreadsheets, databases, and graphics. OpenOffice suite…
Read MoreYour systems carry a lot of confidential and important data. One of the most effective ways to protect and safeguard your system from unauthorized access is to use…
Read More