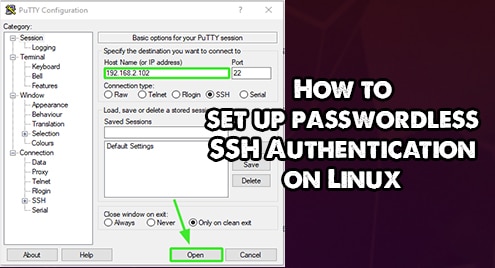
How to set up passwordless SSH Authentication on Linux
Passwords are becoming vulnerable with the ever-evolving cybersecurity environment. No more than ever, systems are becoming prone to brute-force attacks. Users are also making it easy for hackers…
Read More